Overview
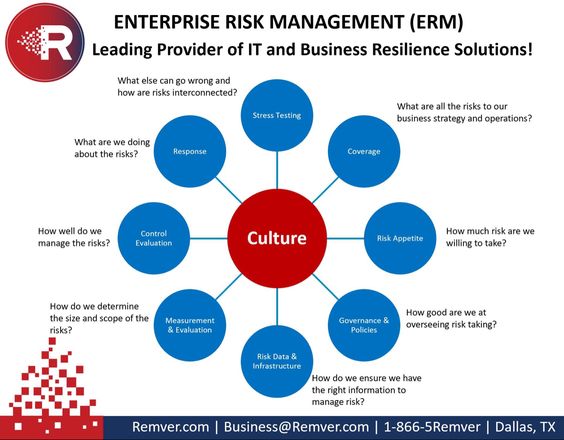
Enterprise risk management (ERM) is an integrated approach to managing the risks of an organization. It is a process that helps organizations identify and manage potential risks associated with their operations, assets, and objectives. ERM is a proactive approach to managing risk that is based on the principles of transparency, accountability, and collaboration. It is an important part of any organization’s risk management strategy and is essential for effective decision-making.
The purpose of ERM is to ensure that risks are identified, assessed, managed, and monitored in a systematic manner. ERM is also used to identify and mitigate potential threats to an organization’s information technology (IT) security. In today’s digital world, IT security is a critical component of an organization’s overall risk management strategy.
Key Components of ERM
ERM is composed of several core components, including risk identification, assessment, control, monitoring, and reporting.
Risk identification is the process of identifying potential risks to an organization’s operations, assets, and objectives. This includes identifying potential threats to an organization’s IT security.
Risk assessment is the process of evaluating the likelihood and impact of identified risks. This includes assessing the potential risks to an organization’s IT security.
Risk control is the process of implementing measures to mitigate identified risks. This includes implementing measures to protect an organization’s IT security.
Risk monitoring is the process of regularly reviewing and assessing the effectiveness of risk controls. This includes regularly reviewing and assessing the effectiveness of an organization’s IT security measures.
Risk reporting is the process of communicating the results of risk management activities to stakeholders. This includes communicating the results of IT security activities to stakeholders.
Benefits of ERM
ERM provides a number of benefits to organizations, including:
Improved decision-making: ERM helps organizations make better decisions by providing them with a comprehensive view of their risks.
Enhanced risk management: ERM helps organizations identify, assess, and manage their risks in a more effective and efficient manner.
Increased stakeholder confidence: ERM helps organizations demonstrate to stakeholders that they are taking a proactive approach to managing their risks.
Improved IT security: ERM helps organizations identify, assess, and manage potential threats to their IT security.
IT Security Risks
IT security risks can come from a variety of sources, including malicious actors, software vulnerabilities, and system failures.
Malicious actors are individuals or organizations that attempt to gain unauthorized access to an organization’s systems or data.
Software vulnerabilities are flaws or weaknesses in software or hardware that can be exploited by malicious actors.
System failures are errors or malfunctions in an organization’s systems or processes that can lead to security breaches.
ERM and IT Security
ERM is an essential component of an organization’s IT security strategy. It helps organizations identify and mitigate potential threats to their IT security.
ERM can help organizations identify potential IT security risks by:
Conducting risk assessments to identify potential threats and vulnerabilities.
Implementing measures to protect against identified threats and vulnerabilities.
Monitoring IT security systems and processes to ensure they are functioning properly.
Reporting IT security risks and incidents to stakeholders.
ERM Best Practices
Organizations should develop and implement a comprehensive ERM program to ensure their IT security is properly managed. The following are some best practices for implementing an effective ERM program:
Develop a risk management strategy: Organizations should develop a comprehensive risk management strategy that outlines the objectives, scope, and approach of the ERM program.
Identify and assess risks: Organizations should identify and assess potential risks to their IT security, including malicious actors, software vulnerabilities, and system failures.
Implement risk controls: Organizations should implement measures to mitigate identified risks, including implementing technical, administrative, and physical security controls.
Monitor and report on risks: Organizations should regularly monitor and report on their IT security risks and incidents.
You might find these FREE courses useful
- Program Risk Management in ClickUp
- Risk Management in Personal Finance
- Investment Risk Management
- Market Risk Management: Frameworks & Strategies
- Credit Risk Management: Frameworks and Strategies
- FinTech Risk Management
- Implementing a Risk Management Framework
- Risk Management Specialization
Conclusion
ERM is an important part of any organization’s risk management strategy and is essential for effective decision-making. It is also an essential component of an organization’s IT security strategy, as it helps organizations identify and mitigate potential threats to their IT security. Organizations should develop and implement a comprehensive ERM program to ensure their IT security is properly managed.